[ad_1]
A new version of the Prometei botnet has infected more than 10,000 systems worldwide
The functionality of cross-platform malware is constantly expanding.
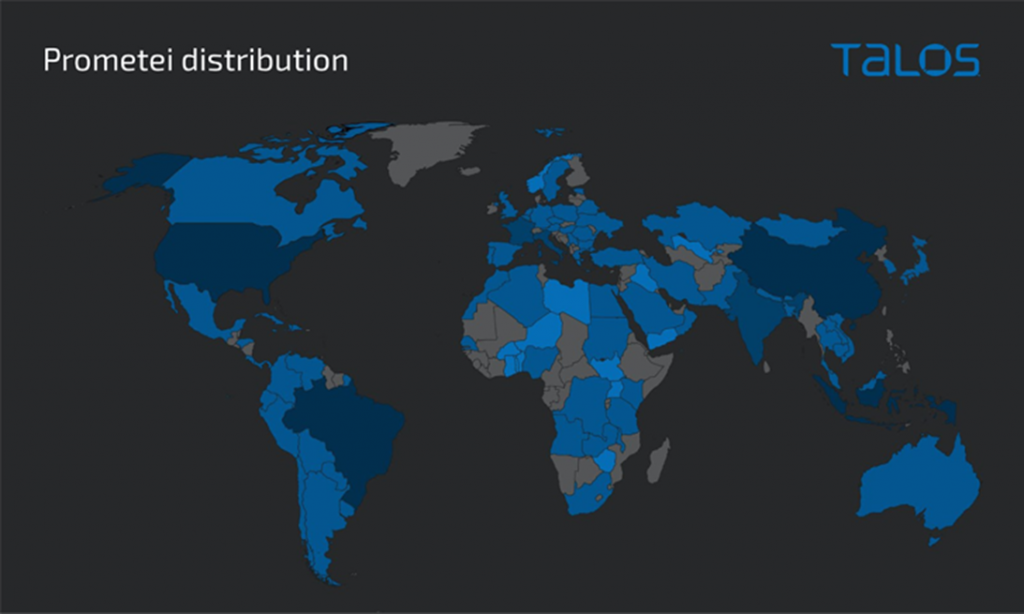
From last November to March of this year, an updated version of the malware botnet Prometei has infected over 10,000 systems worldwide. Infections are both geographically indiscriminate and targeted, with most victims recorded in Brazil, Indonesia and Turkey.
Prometei, first discovered in 2016, is a modular botnet with a large set of components and several methods of distribution, including exploiting vulnerabilities in Microsoft Exchange Server. In the latest variant of the malware, “Prometei V3”, the authors significantly upgraded its stealth in the target system.
The motives behind the spread of the cross-platform botnet are primarily financial in nature, as infected hosts are used to mine cryptocurrency and collect credentials.
Prometei botnet infection map
The attack sequence is as follows: after successfully pinning to the target system, a PowerShell command is executed to download the botnet payload from a remote server. The main Prometei module is then used to get the actual cryptomining payload and other ancillary components.
Some of these helper modules function as distributors designed to distribute malware via Remote Desktop Protocol (RDP), Secure Shell (SSH), and Samba (SMB).
Prometei v3 is also notable for using the Domain Generation Algorithm (DGA) to generate C2-infrastructure. In addition, it contains a self-updating mechanism and an extended set of commands for gathering sensitive data and taking over a host.
Last but not least, the malware deploys an Apache web server associated with a PHP-based web shell that is capable of executing Base64-encoded commands and performing file uploads.
“This recent addition of new features indicates that the Prometei operators are constantly updating the botnet and adding new features.” researchers said companies Cisco Talos .
[ad_2]
Source link
www.securitylab.ru