[ad_1]
Cybercriminals attack law firms with GootLoader and FakeUpdates malware
According to the researchers, browser-based attacks have overtaken e-mail phishing in recent years.
In early 2023, six different law firms were targeted by two separate malware campaigns. The attackers used the GootLoader and FakeUpdates (also known as SocGholish) programs in their attacks.
GootLoader, active since late 2020, is a first stage loader capable of delivering a wide range of secondary payloads such as Cobalt Strike and various ransomware. For his work, he uses the method “SEO poisoning”to direct victims looking for business-related documents to phishing sites with malware based on JavaScript.
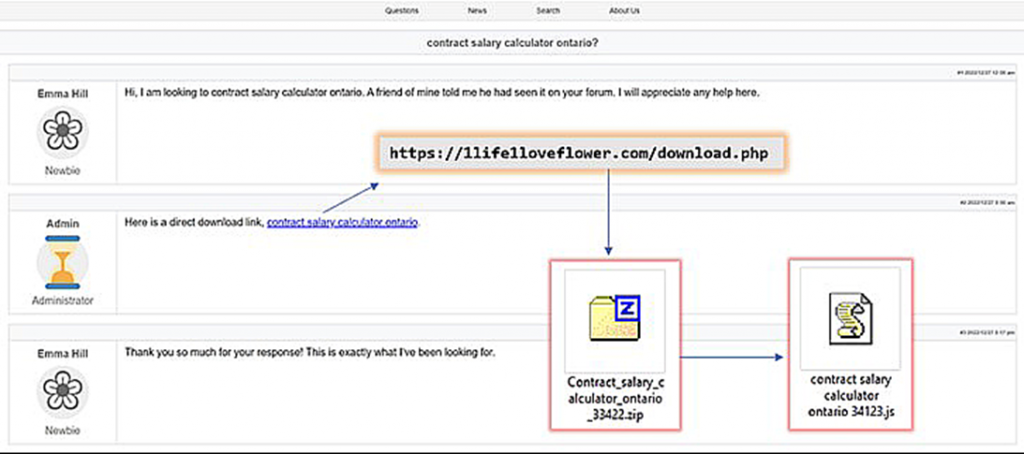
In a malicious campaign detailed eSentire, says the attackers hacked into legitimate but vulnerable WordPress-based websites and added new posts to the forums that would be of interest to potential victims. Of course, these messages contained malicious links.
“When a user navigates to one of the malicious web pages and clicks on a link to download a supposed business agreement, they unknowingly download GootLoader,” said Keegan Keplinger, an eSentire researcher.
The image below shows how an attacker on one of the foreign forums left 3 messages from different accounts: a request to recommend a financial instrument for calculating salaries, a response with a malicious link, and a thank you confirming that the tool works. When a person interested in the same financial instrument sees a dialogue of this kind, he turns off his vigilance and voluntarily downloads a malicious file to his computer.
However, GootLoader is far from the only JavaScript malware targeting the business segment and employees of law firms. Separate malicious campaigns use another malware – FakeUpdates (SocGholish). It allows more executable files to be “dropped” on the target system, and is often distributed using the “Water Hole”.
“Until 2021, phishing via email was the main infection vector used by attackers. But browser-based attacks have shown significant growth in recent years and now fully compete with email as the main vector of infection. This is largely due to GootLoader, SocGholish, SolarMarker, and recent campaigns using Google Ads to rank at the top of search results,” the researcher said. eSentire.
[ad_2]
Source link
www.securitylab.ru